FIDO (Fast IDentity Online) is a security standards alliance (est. 2013) of major consumer electronics and financial companies with the mission of securing personally identifiable information using methods beyond passwords.
Companies such as Samsung, Microsoft and Bank of America are committed to finding better ways to protect your data than traditional passwords which are both cumbersome to the user and easily hackable through modern methods.
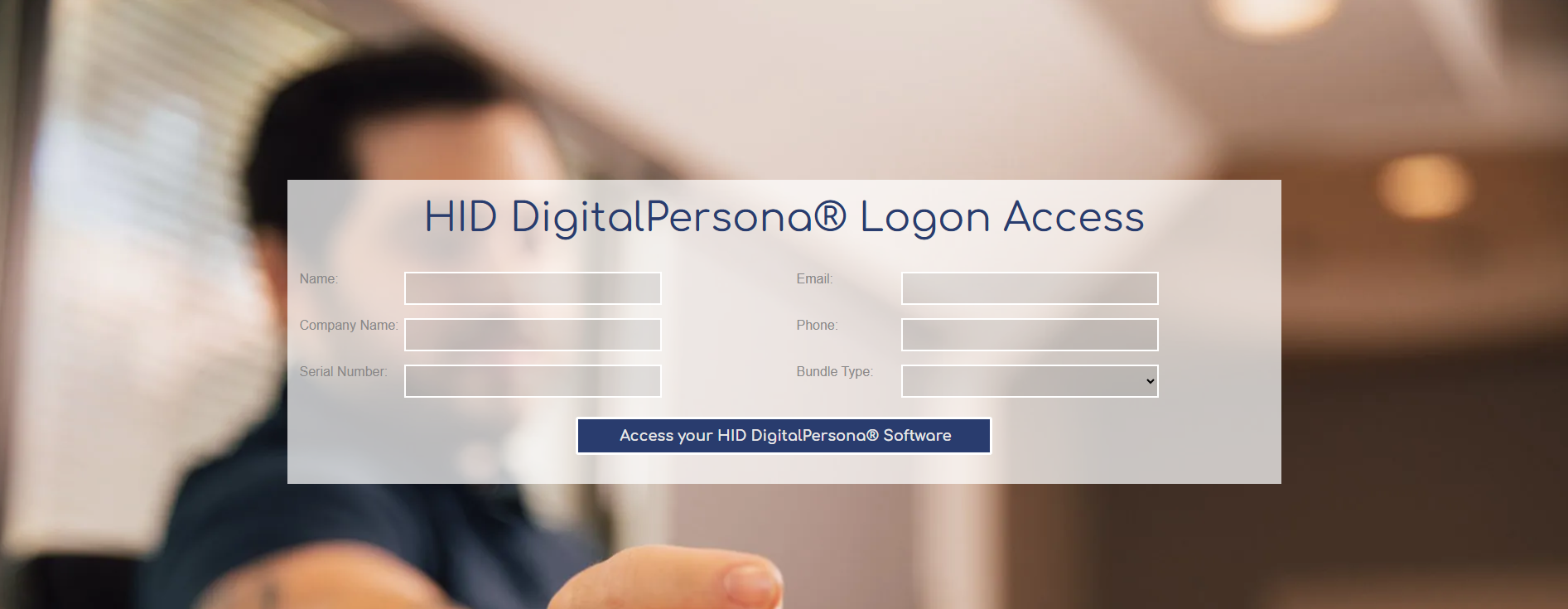
Photo by Felipe Balduino on Pexels.com
Even one of our partners, Thales , is one of the board members and if you don’t know, they are behind the Gemalto line of products (Thales bought Gemalto in 2019) including the IDBridge CT30 , IDBridge CT40 and the IDPrime MD 3810 Dual-Interface Card. Beyond Thales, large Fortune 500 companies have a representative that sits on the board that speaks on behalf of FIDO development. Not all of them have implemented them within their organizations but are readily supporting them such as VISA, USAA, Wells Fargo and Qualcomm ( *Side Note: They are right down the street from where we are located). That is considering the poor quality of passwords that many users have with them.
What are some large companies using the FIDO standard today ?
- Bank of America
- Coinbase
- CVS Health
- Dropbox
- eBay
- GitHub
- Intuit
- Microsoft
- PayPal
- SalesForce
- Target
- Verizon
With the pursuit of developing an open and free standard for both users and corporations, the FIDO Alliance is determined to mature this authentication method and the security token devices used for authentication such as the HID Crescendo Key or the Kensington VeriMark IT Fingerprint Key. This standard will work beyond tech companies though as sectors such as the government and healthcare can take advantage of either securing top secret information to FIPS 201 standards or patients’ documents in relation to the HIPPA standards.
Photo by Jose Francisco Fernandez Saura on Pexels.com
How does Tx Systems know the FIDO Standard?
Tx Systems offers a variety of FIDO-certified security keys from top manufacturers such as HID and Identiv. It is also your choice in smart cards, biometric readers, NFC tags and much more security solutions for your home and business needs. Having been a pioneer in the field since 2001 and our origins in smart cards, we know a thing or two about securing your data and personally identifiable information. We have significant knowledge about FIDO standards! Don’t believe us, we dare you to look at our smart card selection and be amazed at what is there to offer.
What is meant by an open standard?
The difference with an open standard is that it will allow security keys to work across different sites and devices versus a proprietary method that has a limited reach. Proprietary methods would be in the hands of typically, one company rather than ownership among many companies. Think of the Windows operating system whose source code is owned by Microsoft which is protected by copyright with little alterations outside of Microsoft employees. This versus an open-source operating system such as the Linux Kernel which can be edited by anyone without fear of repercussion. Going back to an open standard, the reason that this model is beneficial is that it allows more companies to come onboard without having to invest large amounts of capital for usage rights. With more companies comes more legitimacy in the eyes of the general public who start to adopt it at a larger pace. Users can then submit ideas or throw complaints to improve the FIDO process; thereby, creating a more seamless login process for users while boosting its overall security. An open standard will allow for more accountability and change at a faster rate than relying on one company to make profound changes.
How does the FIDO standard work in practice?
When you open a door to a building, you usually need a physical key to open it, right? This key is usually in your possession on a key ring. Think of it as a way of proving that you are supposed to be in that building. You would technically be trespassing if you were in the building without it.
The FIDO cryptographic-based standard uses something similar to this with a public and private key , so there are two digital keys made. The private key is what you have in your possession such as the security token, the fingerprint or your face which is how you will unlock one door, but there is another one waiting for you which is the public key that the application you are using stores. Think of “public” meaning that it is out in the open whereas “private” is a key that only you know. With this login scheme, you are actually creating a new set of login credentials each time that you login meaning that you avoid common password hacking methods such as password theft and replay attacks. NONE of the information (private key type or authentication hardware type) that you use is stored on the site’s server and rather stays with the hardware device , so if for example, Facebook’s servers are hacked and users’ login information is leaked then you will be good to go as they do not have your fingerprint reader or FIDO security token.
Photo by Wiredsmart on Pexels.com
Given this procedure, you cannot be tracked across multiple online websites when signing in which is currently seen with signing in, for example, with a Google account to a Canva account. It certainly makes it easier than trying to remember a password though. However, with the FIDO Standards, marketers who use targeted ads will have a harder time as they cannot share user data with each other! Darn!
What makes up the FIDO2 Standards?
This supports building the FIDO standards into a browser API essentially it means that browsers will be able to support your FIDO-certified devices such as security keys from the get-go. Say goodbye to trying to program it yourself or installing a “trust-worthy” plug-in.
This supports the usage of hardware-based authentication devices such as FIDO security keys ( Identiv uTrust FIDO2 Security Key ) and mobile devices ( HID Seos ) with the use of WebAuthn-supported browsers as mentioned above.
This supports the use of hardware-based FIDO-certified devices as a means for multi-factor authentication (MFA). So, you could still use your username and password, but a FIDO-device (Hypersecu HyperFIDO Titanium Security Key) as another way of authentication. With this added security, web applications can use an even simpler password scheme such as a four-digit PIN code with their security key.
For more information on the FIDO Alliance, take a look at What is FIDO?
How do I register my FIDO Key on supported websites or applications?
Within every site, there is usually a profile icon ( upper right-hand corner ) that allows you to change your password or other personal information such as your name, email address or telephone number. This tends to be found in the Settings/Privacy/Account Information area. Within this, you may find a security tab or security options side panel, this is usually where you can register your security key such as the HID Crescendo Key which will replace the password that you are SO keen on entering. It may prompt you to verify your identity with an additional verification method such as an SMS or email code.
Once verified, you might also be able to pair a PIN code or fingerprint reader with the security key as a multi-factor authentication (MFA) method for an added layer of security. It may be good to include your email address or phone number to have an additional way of accessing your account should you forget your security key.
*You can have either a single verification method such as a fingerprint, tap or iris scan or do a combination of two for added multi-factor authentication (MFA) security.
How do I logon to my online account or desktop application with the FIDO key?
Make sure to have you FIDO security key (Identiv uTrust Contactless Smart Card Token Pro) or other authentication method such as an OTP (one-time password) device ( HID ActivID MiniToken series ) that generates numerical codes or time stamps, and go to the website’s login page. Once entering your email, you will be prompted to verify your user identity with your registered FIDO device (a.k.a. Private Key ). Tap the security key with your finger, scan your fingerprint for biometric readers or enter your OTP code to login to your account. From here, you should be good to go as the web application has verified your identity using the public key that it has on file. You can now access the site.
Does Tx Systems sell FIDO-certified security keys?
Tx Systems actually sells FIDO-certified security keys such as:
**It is good to note that you can actually use the same security key across multiple accounts, so it will save you from dropping a couple of racks to cover all the accounts that you have.
- HID Crescendo C2300 *DUAL-INTERFACE* FIDO Contact Smart Cards
- HID Crescendo FIDO Key
- Hypersecu HyperFIDO Titanium PRO FIDO2 USB 3.0 Security Key
- Hypersecu HyperFIDO Pro Mini USB 2. Type-A Security Key
- Identiv uTrust FIDO2/PIV NFC USB 2.0 Security Key
- Identiv uTrust Token Pro Mini
- Identiv uTrust Contactless Smart Card Token Pro
- Kensington VeriMark Fingerprint Key
- Kensington VeriMark IT Fingerprint Key
*Luckily, if you have an older FIDO-certified security key, it will continue to work with the online services that you use if they support the WebAuthn and FIDO UAF. This is thanks to the Open Standards ideology that is supported by the FIDO Alliance which eliminates previous proprietary strains on software development and hardware manufacturers who were limited by budget or legal constraints.
**You can also use the HID Crescendo FIDO Key with PKI, FIDO or OATH standards.**

 IT Fingerprint Key
– FIDO2/WebAuth, Windows Hello
IT Fingerprint Key
– FIDO2/WebAuth, Windows Hello & Windows Hello for Business
& Windows Hello for Business
Consumers and corporate entities will not have to worry about their security keys and OS support because there is native support in BOTH Android and Windows 10 devices . So, not only can you use them on your desktop, but you can use them on your mobile devices. If desktop-based application are not your forte then you can also use them on browsers such as Chrome, Edge, Firefox and Safari .
What makes the FIDO standard SO STRONG?
This FIDO standard is based on PKI or Public Key Cryptography which means that it is RESISTANT to phishing and other common attacks that can easily access traditional password schemes. Hackers have a multitude of tools that they use to test your password combination which means that “ABC1234” is not going to cut it when trying to protect your bank account information.
Take a look here for some of the nefarious tools that hackers use to steal your account information. By understanding some of their methods, you can better defend yourself against their trickery and start to fight back.
FIDO supports many different types of authentication methods.
These account authentication methods include facial recognition, fingerprints and voice activation . These are considered under biometrics which offer increased security versus traditional passwords. It takes much more time for a hacker to steal a fingerprint or take a picture of you because they would have to literally follow you around just to take it. Imagine a person trying to take a picture of you to use on your phone to unlock. It seems quite unlikely.
Photo by Matheus Bertelli on Pexels.com
ADOPT FIDO TODAY
In conclusion, the goal of this standard is for it to be both secure and easily accessible. The best of both worlds! .
So are you ready to start using a FIDO-certified security key for your online accounts then take a look at the great deals that we offer on our website. There is much to choose from and great for a wide variety to login to the websites that you use on a daily basis.